Command Access Technologies is a Manufacturer and modifier of high quality electric locks, panic hardware, power transfer products, power supplies and support components.



Access Control
Integrated Technology Solutions is proud to be a single source for your physical security needs. We have qualified engineers and Field Technicians to assist you with application designs, installation, and technical support. Providing you sophisticated solutions with simplified success.
Who, Where, When
Access Control can simply be defined as a method of controlling and reporting on who can go where and when. Access control is implemented to complement and enhance safety and convenience, in addition access control prevents the unauthorized entry of facilities, maintain control of employees, visitors and protect company assets. It regulates the movement of people and products to meet the operational needs of a facility.
Access Control can be achieved by the installation of a simple mechanical lock and key, scalable all the way up to high tech multi-authentication biometric devices integrated to an electronic auto door operator with alarm monitoring real time communication as well as full integration into time schedules to initiate a partial or complete building lockdown.
Access Control Systems Reasons Why
Why implement an Access Control System?
- Minimize human error
- Minimize issuing keys and re-keying of doors
- Automate personnel tracking/audit trail
- Provide complete controlled access to the facility
- Improve building ADA compliance (ADA linked to card holder for ease of access)
- Implement Security Protocol & Policy, access level hierarchy based on personnel responsibility
- Creates and ensures accountability of personnel’s access to the facility (card holder is less likely to pass their card to someone vs. a key because the are directly associated with their card)
- Provides ability to deactivate a card access instantaneously (no need to retain card for security purposes)
- Provides ability to create time schedules (ensures doors are locked/unlocked at appropriate times)
- Provides ability to lockdown entire areas quickly at high threat levels
Automated Advantages
- Improve response to Crisis Management Team
- Take complete and orderly control of your facilities
- Eliminate the need to man all access points
- Real-time visibility of personnel movement and access
- Provide safety for employees and visitors
- Eliminate the buddy system
- Automate and enhance the identification process
- Archive records and create reports for potential future use
- Monitor alarm and event notifications
- Establish and implement access rules
Open Option Access Technology

Open Options provides complete access control systems to numerous integration partners for resale both domestically and internationally. In addition to their core products, OO is known for their ability to rapidly develop customized solutions and to provide end users driven feature enhancements as standard product offerings to their entire customer base.
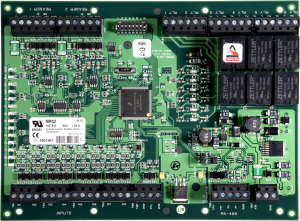 Open Options is a value-added reseller of Mercury Security, which supplies true open hardware platform panels with the most extensive feature set and the world’s largest install base with over 3 million controllers. The fact that multiple manufacturers support this hardware platform is what makes it OPEN and allows the end user a valuable CHOICE in software.
Open Options is a value-added reseller of Mercury Security, which supplies true open hardware platform panels with the most extensive feature set and the world’s largest install base with over 3 million controllers. The fact that multiple manufacturers support this hardware platform is what makes it OPEN and allows the end user a valuable CHOICE in software.


BE WARY OF PROPRIETARY HARDWARE
Not all access control manufacturers carry open hardware, and some carry a mix of proprietary and open panels. Open Options only sells Authentic Mercury OPEN PLATFORM hardware and encourages end users to know what they are buying when it comes to their security system infrastructure.
We believe in the value of open hardware platform products. Integrated Technology Solutions is partners with Open Options.
Integrated Technology Solutions Inc. provides sales, installation & support for video surveillance, access control systems, security cameras & structured cabling. ITS has offices in Milwaukee & Brookfield Wisconsin and Schaumburg, Illinois. Serving the greater Milwaukee Wisconsin Metro Area including: MKE Third Ward, MKE Fifth Ward, Oak Creek, Elkhorn, North Shore, Shorewood, Oconomowoc, Port Washington, Kenosha, Mequon, West Milwaukee Brown Deer, Greendale, Hales Corners, Cudahy, Racine, Brookfield, Beloit, Greenfield, Menomonee Falls, Franklin, Sussex, Fort Atkinson, Cedarburg, Burlington, Glendale, Whitefish Bay, Fox Point, River Hills, Bayside, Wauwatosa, West Allis, St. Francis, MKE, North Milwaukee, and South Milwaukee.
Serving the Chicago, Illinois Area including: Schaumburg, Aurora, Bolingbrook, Buffalo Grove, Evanston, Des Plaines, Oak Park, Oak Lawn, Hanover Park, Elgin, Elk Grove Village, McHenry, Northbrook, Rockford, Romeoville, Spring Grove, Vernon Hills, Wheeling, IL, & the greater Chicago surrounding areas.